Managing the ARCAD-API Server
The ARCAD-API Studio must connect to the ARCAD-API Server to access and store all the elements required to use ARCAD-API.
The ARCAD-API Studio is set up to automatically connect to the server installed at this location: http://localhost:5260. This is because this is the default location/port in which the server is installed if both the server and the studio are installed at the same time on the same machine.
If the server is installed in the default location, there are no connection parameters to define. You can connect to the server directly.
Follow the subsequent steps to connect to a different ARCAD-API Server if you did not install the server in the default location.
Step 1 Click the ![]() server connection icon in the
server connection icon in the ![]() navigator to open the Connection Properties dialog.
navigator to open the Connection Properties dialog.
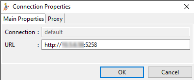
Step 2 Define the following fields in the Connection Properties dialog. Click OK.
- Connection
- This field displays the default name of the ARCAD-API Server connection.
- Address/IP & Ports
- Define the address where the ARCAD-API Server is located, including its appropriate port. The default HTTP port is 5260, and for secure connection, the default HTTPS port is 52600.
- Proxy (tab)
- [Optional] When this box is checked, an HTTP proxy is used to connect to the ARCAD-API Server. All the Proxy connection fields must be defined.
Follow the subsequent steps to connect the ARCAD-API Studio to the ARCAD-API Server.
Step 1 Click the ![]() connection icon in the
connection icon in the ![]() navigator to connect to the ARCAD-API Server.
navigator to connect to the ARCAD-API Server.
Step 2 Define the Username and Password.
Initially, the administration-level login must be used. This default generated admin-level user has access to all of the ARCAD-API features.
| Login | admin@quadra |
| Password | quadra |
Click Connect.
Result The ARCAD-API Studio is connected to the ARCAD-API Server and is ready to be used.
To change users, click the ![]() Connection icon in the navigator. Connect to the ARCAD-API Server using a different Username and Password.
Connection icon in the navigator. Connect to the ARCAD-API Server using a different Username and Password.
This section does not describe the configuration required for TLS in the ARCAD-API Server. The TLS configuration belongs to the AFS configuration layer. Refer to the ARCAD-API Server Configuration Guide.
For security reasons, you may need to use an encrypted connection between the server and the studio. To do this you must activate the use of the HTTPS protocol, by checking the Use HTTPS option in the server connection parameters. However, this protocol, based on the TLS network protection layer, must be correctly configured to be implemented. Depending on the server settings, the client program will have to validate the server's TLS certificate and potentially use its own key.
In most cases, only the validation of the server certificate is required. If this certificate is the product of a chain of trust whose root is a recognized Certification Authority (CA) then there is nothing special to do on the client side. The Java virtual machine already recognizes and approves certificates from all the parties in the market. However, if the server's certificate was not issued by a CA, or your organization uses a specific CA, it is necessary to add the certificate of this CA, or directly the server's certificate in the studio configuration.
It is also possible that the server has been configured in such a way that the studio must also use a key pair (private, public) that requires the server to validate the studio's certificate.
In case the server uses a certificate that is not issued by a CA or requires the studio to use a key pair, the administrator will pass these materials to you. The most secure way to do this is to send them to you in a container, called a KeyStore, which is password protected. In case the HTTPS connection requires both the validation of the server's certificate and a key pair for the studio, it is possible that the administrator will send you two stores, one containing the certificate to be approved, this is called a TrustStore, the other containing only the studio's key pair. This last store keeps the name KeyStore.
It is also possible that the administrator transmits the certificate directly to you, without integrating it into a store, in this case make sure that the source of the transmission is not spoofed. Integrating the wrong trusted certificate can jeopardize the security of the entire installation.
Certificates and key pairs have a limited validity period. This period varies, generally from 1 to 12 months. The following configuration procedure must therefore be repeated each time the equipment is updated. Knowing that an expired certificate or key pair will block the connection to the server.
Once you have the KeyStore(s) and their respective passwords, or, if not available, the server certificate, follow the steps below to redefine the HTTPS protocol settings:
Step 1 To access the TLS Settings dialog, ![]() TLS Settings
TLS Settings
Step 2 Edit the absolute paths to the TrustStore and KeyStore and their corresponding passwords.
Step 3 Click the Import Certificate button to import your own certificates into the file indicated in the TrustStore path.
You can click the Import Certificate button to import the server's certificate if it was sent to you as is. It will be included in the TrustStore defined in this window.
Step 4 Click OK to save your changes or Cancel to keep the default settings.
The Reset button resets access information and passwords to the default values provided by the ARCAD-API Studio.
To configure the ARCAD-API Server, ![]() configure icon in the navigator
configure icon in the navigator
For more information, refer to Configuring the ARCAD-API Server.
To manage the ARCAD-API Server preferences, ![]() preferences icon in the navigator
preferences icon in the navigator
For more information, refer to Preferences.
To view a server’s log, right-click on it in the ![]() Connections list then select
Connections list then select ![]() Server Log.
Server Log.
To verify the version of a![]() Server Information icon in the navigator
Server Information icon in the navigator